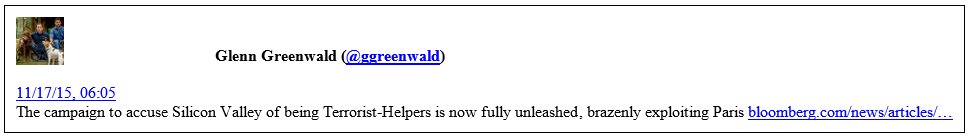
Just as I forecast, the Paris terror event of last Friday is being used to launch an attack on the use of encryption.
The Bloomberg article says:
The bloodshed in Paris led U.S. officials Monday to renew calls for limits on technology that prevents governments from spying on phone conversations, text messages and e-mails.
Senator Dianne Feinstein, a California Democrat, said she asked Silicon Valley companies to help law enforcement and intelligence agencies access communications that have been encrypted — or scrambled to evade surveillance — if terrorists are using the tools to plan attacks.
End of quote.
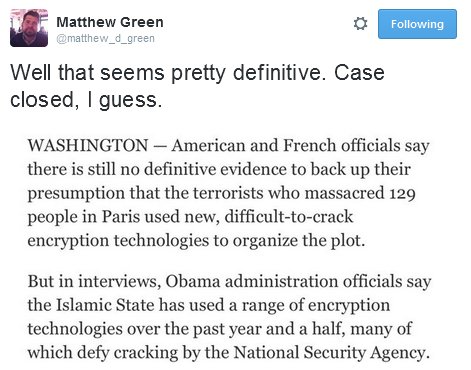
The N.Y. Times went down a similar path, but then removed the article.
Matthew is a Professor of cryptography at Johns Hopkins University and a regular commentator on such matters.
Of course, the public dialogue does not consider the real evidence, but let’s consider some. This study looks at whether there has been any apparent increase in the use of cryptography by on-line jihadists since the Edward Snowden revelations:
- The underlying public encryption methods employed by online jihadists do not appear to have significantly changed since the emergence of Edward Snowden. Major technological recent advancements have focused primarily on expanding the use of encryption to instant messenger and mobile communications mediums.
- Aside from warning of tampered copies of “Asrar al-Mujahideen” that were deliberately infected with spyware, none of the prominent jihadi logistical units have expressed any public doubt as to the continued effectiveness of encryption methods employed in their software packages that were released prior to the Snowden leaks.
- The actual release of new jihadi-themed encryption software packages, like “Asrar al-Dardashah,” seems to have had a far more noticeable impact in terms of driving waves of interest in the subject of encryption among users of jihadi web forums than the publication of the Snowden NSA revelations in June 2013.
- Well prior to Edward Snowden, online jihadists were already aware that law enforcement and intelligence agencies were attempting to monitor them. As a result, the Snowden revelations likely merely confirmed the suspicions of many of these actors, the more advanced of which were already making use of – and developing – secure communications software.
End of quote.
But this is not about the facts. It’s about justifying to the public the elimination of any encryption that stops the global elite and their proxies, the state, monitoring everything we say and do.
I wonder how much of a fight Apple will put up. Or are they just shadowboxing?
Recent Comments